For banks, VASPs, and other highly regulated financial institutions, the challenge is rarely just compliance. It is operationalizing compliance without creating a fragile, high-maintenance architecture around your most sensitive data.
For organizations whose internal policies or regulatory interpretations require stricter control over sensitive data, this challenge becomes even more pronounced.
That is the problem CryptoSwift Outpost is designed to solve.
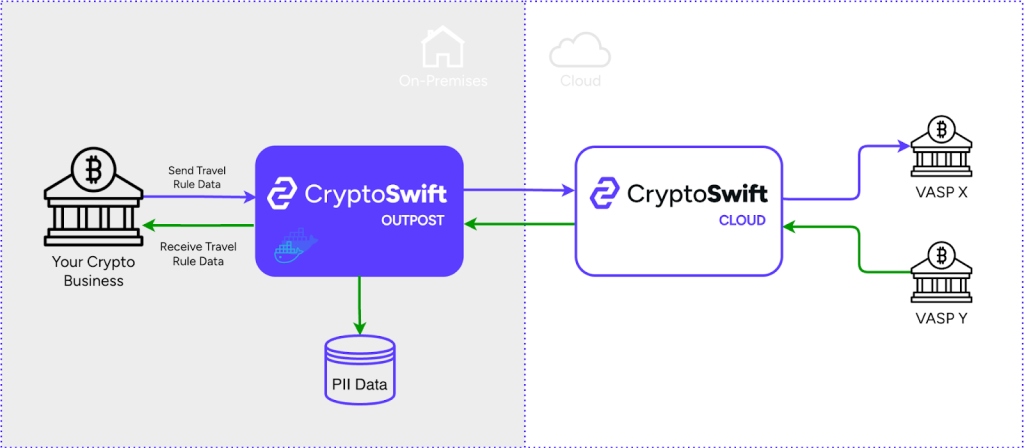
CryptoSwift Outpost is a single-tenant, on-premises edge service that can be deployed when institutions need to keep Travel Rule PII within their own infrastructure, while still using the CryptoSwift platform for core transaction processing. In practice, that means sensitive customer data remains under your control within your environment and your SQL database, while CryptoSwift continues to power the transaction workflows around it.
The result is an operating model aligned with the needs of more stringent environments: strong data control, clear deployment boundaries, and a significantly simpler system to maintain compared to heavyweight alternatives often associated with on-premise requirements.
Why this matters for regulated entities
For many institutions, “cloud-enabled” is acceptable, but “cloud-only for sensitive PII” is not.
Travel Rule data sits in one of the most sensitive categories of operational data. It includes personally identifiable information about originators and beneficiaries, and it often falls under overlapping internal security policies, data residency requirements, outsourcing controls, audit expectations, and legal review. Even where cloud use is permitted, regulated teams still want the most defensible answer to a simple question: Where does the sensitive data live?
With Outpost, the answer is straightforward: the Travel Rule PII datastore lives on-premises, inside your environment, under your control.
That matters because it changes the conversation with risk, compliance, security, and internal audit. Instead of asking them to accept a fully outsourced storage model for sensitive data, you can present a controlled architecture where:
- Outpost runs inside your infrastructure
- the SQL database storing Travel Rule PII runs inside your infrastructure
- the deployment is single-tenant
- CryptoSwift handles core transaction processing, while your local environment remains the holder of the sensitive Travel Rule record
For regulated institutions, that is a meaningful architectural distinction.
How Outpost works
Outpost sits between your internal systems and the CryptoSwift cloud API.
Your systems integrate with Outpost as their edge endpoint. Outpost then proxies most traffic upstream, but it handles Travel Rule PII differently: it stores that data locally and links it to the corresponding transaction.
CryptoSwift Outpost: PII data remains on-premises, while
Outgoing transactions
When your system submits an outgoing transaction through Outpost:
- Outpost receives the full transaction payload.
- It stores the originator and beneficiary data locally in your SQL database.
- It forwards the transaction to the CryptoSwift cloud API for transaction processing.
- When the cloud API returns the transaction identifier, Outpost links the local PII record to that transaction.
- If the upstream request fails, Outpost does not silently lose the local state. It marks the record as failed and preserves the operational trail.
That last point is important. In many integrations, error handling around sensitive side data becomes an afterthought. Outpost is designed to keep a durable local record and explicit status transitions, rather than relying on brittle happy-path assumptions.
Incoming PII forwarding
For incoming Travel Rule data, the flow works in the opposite direction:
- CryptoSwift forwards the incoming PII payload to Outpost.
- Outpost verifies the request signature before trusting the payload.
- The PII is stored locally in your SQL database.
- Outpost returns the corresponding transaction identifier.
This gives institutions a consistent model for both outbound and inbound Travel Rule data: local persistence, controlled linkage, and auditable handling.
Transaction retrieval and enrichment
Outpost also solves a practical usability problem.
When a client requests a transaction by ID, Outpost first fetches the transaction from the CryptoSwift cloud API. If there is a matching local PII record, Outpost injects the locally stored originator and beneficiary data into the response before returning it.
So users and internal systems can still work with a complete transaction view, while the sensitive data remains managed locally. The cloud platform can do what it is good at, and your on-prem environment remains the source of truth for Travel Rule PII.
What makes Outpost different
Many on-prem solutions for regulated workloads become difficult not because the idea is wrong, but because the architecture is too large, too distributed, or too customized to operate cleanly over time.
Outpost takes a different approach: it is intentionally small.
At its core, the deployment model is simple:
- one single-tenant service
- one SQL database
- one clear upstream integration with the CryptoSwift cloud API
- containerized delivery via Docker
- environment-based runtime configuration
- a standard health endpoint for monitoring and orchestration
That simplicity is not cosmetic. It is the reason Outpost is easier to maintain than many comparable on-prem offerings.
There is no sprawling control plane to own. No large cluster of bespoke infrastructure components. No need to re-create an entire SaaS platform inside your environment just to satisfy a PII storage requirement.
Instead, Outpost concentrates on one job: acting as the controlled local edge for sensitive Travel Rule data.
Architecturally, it is also cleanly separated. Proxying, PII storage, transaction enrichment, configuration, logging, and persistence are split into focused components. Storage sits behind a repository abstraction, which means changes to the underlying persistence model can be made without reworking the entire service, allowing for a wide range of different database engines to be used with Outpost. Regulated deployments do not just need to launch; they need to stay supportable.
Security by design, not by marketing language
Security claims only matter when they are reflected in the way the service actually behaves.
Outpost includes several concrete controls that are especially relevant in regulated environments.
Signed incoming PII forwarding
Incoming PII forwarding is authenticated with HMAC-SHA256 using a dedicated shared secret. Outpost verifies the signature over the exact raw request body, not a re-serialized approximation. It also enforces a timestamp tolerance window to reduce replay risk and uses timing-safe comparison for signature validation.
That gives institutions a clear, defensible control around cloud-to-on-prem PII forwarding.
Controlled deployment boundary
Outpost is single-tenant and deployed inside the client environment. That reduces multi-tenant exposure concerns and gives infrastructure, security, and audit teams a much cleaner deployment story.
Hardened edge behavior
The service uses standard HTTP hardening, validates runtime configuration at startup, supports trusted reverse-proxy deployment, and exposes a straightforward health endpoint for monitoring and operational checks.
Operational traceability
Outpost does not treat failures as invisible side effects. It keeps explicit local record states, including pending, linked, stored, and upstream-failed conditions. For regulated operations teams, that improves observability and incident handling.
Why banks should care
Banks do not need another “flexible platform” that quietly pushes sensitive data governance into the implementation phase.
They need infrastructure that aligns with how regulated technology decisions are actually made:
- keep sensitive customer data under institutional control
- minimize architectural sprawl
- make security controls explicit
- preserve operational auditability
- reduce the maintenance burden on internal engineering and infrastructure teams
That is where Outpost fits.
It gives regulated institutions a pragmatic middle path. You do not have to choose between a cloud-only model for sensitive Travel Rule data and a large, expensive, custom on-prem build. You can keep the sensitive PII record on-prem, keep the deployment model simple, and still benefit from CryptoSwift’s cloud transaction processing.
The practical value of a smaller architecture
In highly regulated environments, maintainability is not a convenience issue. It is a risk issue.
Every additional moving part increases the cost of patching, validating, monitoring, documenting, and defending the deployment internally. Every custom subsystem becomes another item for architecture review, another operational dependency, another audit question.
Outpost avoids that trap by staying focused.
It is lightweight enough to operate cleanly, structured enough to evolve safely, and opinionated enough to solve the actual regulated-data problem without dragging institutions into unnecessary platform ownership.
For teams that need on-prem control without on-prem complexity, that difference is significant.
Conclusion
CryptoSwift Outpost is built for institutions that need a serious answer to PII control.
It keeps Travel Rule PII anchored on-prem in the client’s own environment, while preserving integration with CryptoSwift for core transaction processing. It provides a secure, auditable, single-tenant deployment model. And because its architecture is intentionally narrow and lightweight, it is materially easier to maintain than many traditional on-prem solutions.
For banks and other highly regulated entities, that combination is the point: stronger control over sensitive data, without inheriting a harder platform to run.

